Local Implementations of Non-Local Quantum Gates in Linear Entangled Channel ()
1. Introduction
One of the most striking features of the quantum world is entanglement. This esoteric quantum property has found practical use in the field of quantum information [1] . Qubit teleportation [2] [3] , superdense coding [4] , quantum information splitting [5] , secret sharing [6] , remote state preparation [7] [8] and many other quantum communication protocols have been theoretically and experimentally demonstrated taking recourse to entanglement. Local implementation of non-local quantum gates is another quantum communication protocol implementing a multi-partite quantum gate which can not be decomposed into individual local operations between spatially distributed qubits. This can be achieved using entangled channels shared by the remote parties and local operations with classical communications (LOCC). This quantum task is also called gate teleportation, which is necessary for distributed quantum computing.
As is well known, controlled-NOT (CNOT), together with the single qubit gate, form the universal gates to which other gates can be decomposed [9] . In principle, Controlled-Unitary gates can be implemented locally, using only CNOT gate teleportation protocol. Involving less entanglement and communication costs, several protocols have been proposed implementing non-local multi-partite operations locally by LOCC using entangled channels [10] -[21] and qubit communication [22] [23] . Probabilistic and deterministic gate implementation using non-maximally entangled state has been explicated [24] -[27] . Assisted with linear optical manipulations, photon entanglement produced from parametric down-conversion, and post-selection from the coincidence measurements, the CNOT gate has been teleported experimentally [28] . Later, other experimental protocols have been demonstrated [29] [30] . In contrast with the known protocols, we consider here an arbitrary multipartite state, either product or entangled, where all the qubits are remote placed and demonstrate the protocol of simultaneous and  -qubit controlled operation in linear entangled channel.
-qubit controlled operation in linear entangled channel.
In the familiar network by Eisert-Jacobs-Papadopoulos-Plenio [10] , each of the control parties shares one entangled state with the target party and none of the control parties shares entanglement between them whereas in linear entangled channel, the control parties share entanglement with the adjacent control parties and only one of them shares entanglement with the target party. As this network is linear, the target party has to maintain only one entangled channel, which is particularly useful when the entanglement sharing is difficult between each controlling agent with the target party. In this paper, we start with a three party scenario, where Alice and Bob simultaneously implement controlled-Hermitian  gate to Charlie in linear entangled network, which is then generalized for arbitrary multi-partite state. Next section deals with the implementation of controlledcontrolled-Unitary gate and the generalization to
gate to Charlie in linear entangled network, which is then generalized for arbitrary multi-partite state. Next section deals with the implementation of controlledcontrolled-Unitary gate and the generalization to  -controlled Unitary gate implementation. Finally, we conclude with directions for future work.
-controlled Unitary gate implementation. Finally, we conclude with directions for future work.
2. Simultaneous Implementation of Controlled-Hermitian Gate
Consider three remote parties Alice, Bob and Charlie possess qubits 1, 4 and 7 respectively of the arbitrary state
 (1)
(1)
with . Now Alice and Bob want to implement Controlled-Hermitian Gate (as well as unitary) on Charlie’s system simultaneously where the target qubit is common for both the control parties. To achieve this task, Alice and Bob share a Bell state between their respective qubits 2 and 3; Bob and Charlie share a Bell state between their respective qubits 5 and 6 :
. Now Alice and Bob want to implement Controlled-Hermitian Gate (as well as unitary) on Charlie’s system simultaneously where the target qubit is common for both the control parties. To achieve this task, Alice and Bob share a Bell state between their respective qubits 2 and 3; Bob and Charlie share a Bell state between their respective qubits 5 and 6 :
 (2)
(2)
Here Alice shares entanglement with another control party and Bob shares entanglement with the target party, which makes a linear entanglement connection (shown in Figure 1). The combined state of all the qubits possessed by Alice, Bob and Charlie is given by,
 (3)
(3)

Figure 1. Simultaneous implementation of Controlled-Hermitian gate through linear network.
The details protocol of simultaneous  implementation through linear network is described belowStep 1: Alice first applies controlled-NOT gate
implementation through linear network is described belowStep 1: Alice first applies controlled-NOT gate  on her qubits 1 and 2.
on her qubits 1 and 2.

Step 3: Bob measures qubit 5 in computational basis and Charlie applies local operations according to the outcomes of the measurements as follows,

Step 4: Finally qubit 3 and 6 are measured in Hadamard basis by Bob and Charlie and corresponding Alice applies unitary operations to obtain the desired state.

Step 2: Then she measures qubit 2 in computational basis and Bob applies unitary gates as follow.
The pictorial representation of local unitary operations, measurements and classical communications of this protocol has been depicted in Figure 1. The simultaneous remote implementation of controlled-Hermitian gate from two parties to one consumes 2 ebits and total 5 cbits to communicate the measurement outcomes. The generalized protocol for  -party of simultaneous
-party of simultaneous  gate implementation described in Figure 2, is an extension of the above protocol. For
gate implementation described in Figure 2, is an extension of the above protocol. For  -party, the communication cost is
-party, the communication cost is  ebits and
ebits and 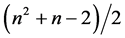 cbits.
cbits.
From the above protocol, it can be inferred that the Unitary as well as Hermitian operators have significance in linear entangled network. This operator has the additional property of involution (i.e., the operator is same as its inverse), which is responsible for making this protocol deterministic. Most of the important gates like controlled-Pauli gates, controlled-Hadamard gate etc., belong to this category, making this implementation powerful.
3. Multiparty Controlled Unitary Gate Implementation
It has been shown that a more general form of Toffoli gate, i.e., controlled-controlled-Unitary gate can be deterministically implemented using two Bell pairs (2 ebits of entanglement) and 4 cbits to communicate the measurement outcomes [10] . Here, we demonstrate the implementation of this non-local gate with the same communication cost using linear entangled channel (shown in Figure 3). For illustration, we consider the same qubit distribution shared by Alice, Bob and Charlie described in Equation (3):
 (4)
(4)
where we want to implement controlled-controlled-Unitary gate,  (here qubit 1 and 4 are control bits and qubit 7 is target bit) on
(here qubit 1 and 4 are control bits and qubit 7 is target bit) on . The details of the protocol is illustrated belowStep 1: Alice first applies controlled-NOT gate
. The details of the protocol is illustrated belowStep 1: Alice first applies controlled-NOT gate , on her two qubits.
, on her two qubits.

Figure 2. Simultaneous implementation of n-party controlled hermitian gate through linear network (Here  denotes the control parties and T denotes the target party).
denotes the control parties and T denotes the target party).

Figure 3. Controlled-controlled-Unitary gate implementation through linear network.

Step 3: Bob measures on qubit 5 in computational basis and accordingly Charlie performs unitary gates, (here  is denoted as
is denoted as ).
).

Step 4: After that Charlie measures qubit 6 in Hadamard basis and Bob applies local operations depending on the outcomes.

Step 5: Finally qubit 3 is measured in Hadamard basis and Bob performs unitary gates to get the desired state which is shared by three parties.
The above procedure can be generalized to implement a  -qubit gate, where
-qubit gate, where  qubits are controls and the unitary operator acts on the target qubit, only if, all the control qubits are
qubits are controls and the unitary operator acts on the target qubit, only if, all the control qubits are  s. The protocol is illustrated in Figure 4 and for
s. The protocol is illustrated in Figure 4 and for  -party gate the communication cost is
-party gate the communication cost is  ebits and
ebits and  cbits which is optimal as shown in [10] .
cbits which is optimal as shown in [10] .
4. Conclusion
In conclusion, we have described non-local gate implementation protocols in linear entanglement network by LOCC. Although the classical communication cost for implementing simultaneous controlled-gate is more as compared to the scenario in [10] , the linear network is advantageous for large , as each party shares only two
, as each party shares only two
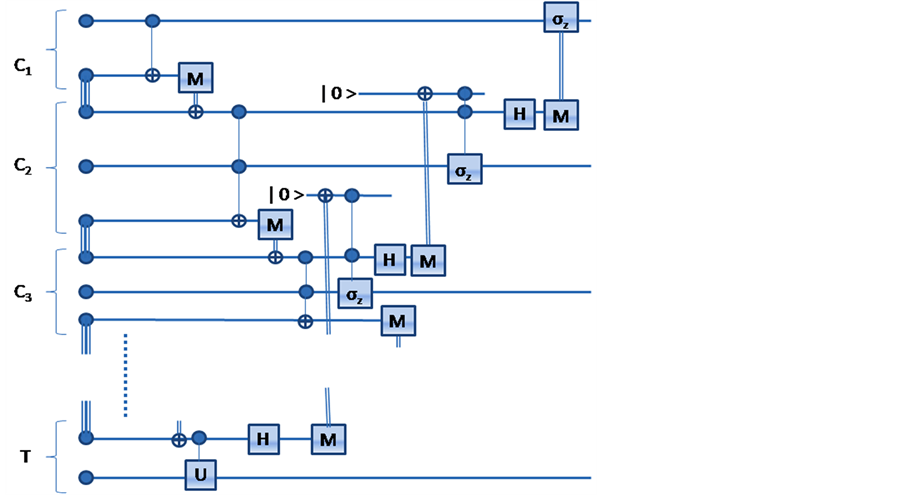
Figure 4. N party Controlled-Unitary gate implementation.
entangled states and the target as well as the first control party share one entangled state. The fact that, our network comprises of Bell states, which are realized in laboratory conditions, makes our protocol experimentally achievable [3] . Optimal protocol for the simultaneous controlled-Unitary and other non-local gate implementations in linear entangled channels can be further investigated.
Acknowledgements
The authors acknowledge Prof. Vijay A. Singh of Homi Bhabha Centre for Science Education (HBCSE-TIFR), Mumbai, India for continuous encouragement. This work is supported by the “National Initiative on Undergraduate Science” (NIUS) program, undertaken by HBCSE.
We acknowledge that summary of this work is presented as a poster in “Asian Quantum Information Science Conference 2013”.