A Novel Technique for Detection of Time Delay Switch Attack on Load Frequency Control ()
1. Introduction
Modern power grids rely on telecommunication technologies for control and monitoring, in a way to improve efficiency and reliability distribution. However, their reliance on computers and multi-purpose networks makes them vulnerable to cyber-attacks [1] -[3] . Recently, the investigation of attack methods on industrial control systems and their countermeasures have been the focus of many academic, industries, and governments. Here, we will investigate one type of attacks on a power control system recently proposed by Sargolzaei et al. [4] -[6] that is time delay switch attack and we provide a simple detection/estimation technique for time delays caused by an adversary. State estimation is one of the pivotal features of future power systems [7] . According to [8] , improving the resiliency and reliability of smart distribution networks could be obtained via deploying renewable resources and demand side management programs. As it has been mentioned in [9] , demand response can ameliorate the load curve by motivating smart customers utilizing smart communication infrastructure and smart meters.
The controller design for systems with time delay is one of the interests of many researchers [10] -[12] but they have not studied that time delay can be injected to the system as an attack. Time delays injected by a hacker in a control system would, in general, destabilize the system or cause inefficiency in performance of the system. This is a new attack in the context of power systems (e.g., load frequency control (LFC)) on networked control systems (NCS) [13] and is named time-delay-switch attack or TDS for short [4] . To avoid possible damage of TDS attacks, systems and controllers must be redesigned in a way to detect and correct for variable time delays.
Time delays exist in power systems, in the sensing and control loops. The traditional controllers of power systems are designed based on current information being available and ignoring time delays even if they present. However, power grids technologies are continuously being improved by introducing new telecommunication technologies for monitoring to improve efficiency, reliability and sustainability of supply and distribution. For example, the introduction of a wide area measurement system (WAMS) provides synchronized near real-time measurements in phase measurement units (PMUs). WAMS which are used for stability analysis of power systems can also be used for designing more robust controllers. Nevertheless, time delays are present in PMUs measurements as a result of natural transmission lines [14] .
Several studies have considered the problem of stability of power systems with time delays [10] [11] . The impact of time delays on the power system controllers was discussed in [15] -[19] . In [20] , authors studied the effects of delays on the small signal stability of power systems. In [15] and [16] , methods to eliminate oscillations that resulted from time-delayed feedback control were proposed. Authors in [21] presented a wide-area control system for damping generator oscillations. Using phasor measurements, but with delays, a controller was proposed in [14] and small signal stability of the power system was considered. A feedback controller designed for power systems with delayed states was proposed in [22] . This controller deals with the combined effects of the instantaneous as well as delayed states using the quadratic Lyapunov function for systems with delays. Additional studies on power systems with delay can be found in [2] [3] [10] -[12] [23] -[25] and the references therein. However, most of these studies considered either the construction of controllers that were robust to time delays or controllers that used offline estimate of time delays. As far as we know, there are no control methods that perform online estimation of dynamic time delays and real time control of power systems. Furthermore, few studies [26] [27] considered control of power systems with time delays introduced by adversary.
In this paper, we will describe a simple yet effective method to address a TDS attack on the observed states of a controlled system. Our method utilizes a time delay estimator, a communication protocol to alarm for time delay switch attack, a buffer to store the history of controller commands and an optimal controller to stabilize or track a reference signal and a local to the plant emergency controller to stabilize the plant if large time delays are detected. For now, we will only deal with LTI systems in state feedback.
2. Method
All control methods developed in the past compensate for time delays either rely on controller robust to a maximum time delay, off-line estimates of time delays or approximation of time delayed signals [26] [27] . Here, we develop an alternative time delay estimator which is simpler and will help with systems under time delay attack. In this paper, we propose a general method for control of systems under TDS attack. We have developed this method for continuous linear time-invariant systems. We have implemented our models and control strategies in MATLAB to demonstrate the performance with simulation.
The proposed method is shown in Figure 1. Its basic elements are: plant model, time delay detector, emergency controller and controller. The controller can either be a PID controller or an optimal feedback controller. The emergency controller’s job is to stabilize the system in case of an attack on the communication lines of the distant controller. The time delay detector estimates the time delay in the communication channel from telemetered data. If the delay is larger than a maximum allowed time delay it sends alarm signals to the controller and emergency controller. If an alarm signal is received by the emergency controller it will begin to operate in a way to stabilize the plant to a desired state while the distant controller stops to operate until the delay is corrected.
Suppose the system we are dealing with is linear time invariant (LTI) or can be approximated in a region of interest by a LTI system,
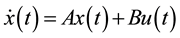 , (1)
, (1)
where x and u are state and control vectors, respectively. Matrices A and B are constant matrices with suitable dimensions.
Then, the solution is given by
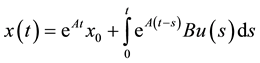 (2)
(2)
with time delay τ, either a time-delay switch attack or a natural delay, the solution of Equation (2) becomes
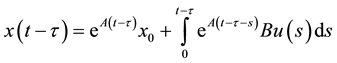 . (3)
. (3)
Let us write the solution  at the time t in terms of the solution with the time delay
at the time t in terms of the solution with the time delay ; we have
; we have
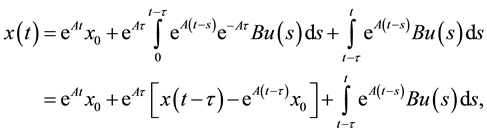 (4)
(4)
In general, the time delay τ is an unknown variable. Let’s assume that τ is slowly varying, compared to the changes in u and x, and  is our estimate of the time delay τ. Then,
is our estimate of the time delay τ. Then,  is the estimation error in the time delay. The predicted state
is the estimation error in the time delay. The predicted state  of the system based on the estimate of time delay
of the system based on the estimate of time delay  is given by
is given by
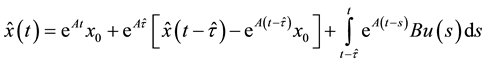 (5)
(5)
where  is the estimate of the delayed state given the estimate of the delay
is the estimate of the delayed state given the estimate of the delay  (i.e. a simulated signal).
(i.e. a simulated signal).
It should be noted that,  is what we actually measures and deliver to the plant model. So, at every instance of time, the variables
is what we actually measures and deliver to the plant model. So, at every instance of time, the variables ,
, ![]() ,
, ![]() , A, B and
, A, B and ![]() are known to the controller and the plant model. On the other hand, the current state
are known to the controller and the plant model. On the other hand, the current state ![]() and the time delay
and the time delay ![]() are unknown. It’s essential that the plant model estimates state
are unknown. It’s essential that the plant model estimates state ![]() accurately. Because of the delay, an accurate enough estimation of
accurately. Because of the delay, an accurate enough estimation of ![]() requires a good estimate of the delay τ. We will show how to estimate the delay τ.
requires a good estimate of the delay τ. We will show how to estimate the delay τ.
![]()
Figure 1. Block diagram of the proposed control system.
The estimation error in states can be described by ![]() and with delay it is given by
and with delay it is given by
![]() . (6)
. (6)
Then the idea is to estimate ![]() overtime as fast as possible to minimize the error
overtime as fast as possible to minimize the error![]() . Using the gradient descent method, we set
. Using the gradient descent method, we set
![]() (7)
(7)
where ![]() is the learning parameter and select
is the learning parameter and select![]() . With some manipulation, we have
. With some manipulation, we have
![]() . (8)
. (8)
Assuming that, ![]() , which is reasonable for initial time, we arrive at
, which is reasonable for initial time, we arrive at
![]() (9)
(9)
Equation (9) is the one we will use to estimate the time delay![]() . However, there are practical issues that we need to consider. Computing machines have finite memory and temporal resolution. Therefore, we are unable to implement Equation (9) without discrete approximation and boundedness assumptions. To guarantee stability of calculations and limit our memory usage we have to add the following condition,
. However, there are practical issues that we need to consider. Computing machines have finite memory and temporal resolution. Therefore, we are unable to implement Equation (9) without discrete approximation and boundedness assumptions. To guarantee stability of calculations and limit our memory usage we have to add the following condition,![]() . This condition will allow us to construct a finite buffer to store the history of
. This condition will allow us to construct a finite buffer to store the history of ![]() from t to
from t to![]() .
.
After designing the time delay estimator, we turn our attention to the controller and emergency controller. The controller can either be a PID controller or an optimal controller depending on the requirements of the application. Equation (10) is the PID controller and Equation (11) is the optimal controller,
![]() (10)
(10)
![]() (11)
(11)
where the error is![]() . Either controller, i.e., the PID or the optimal controller, can be designed in a way to be robust to some maximum time-delay
. Either controller, i.e., the PID or the optimal controller, can be designed in a way to be robust to some maximum time-delay![]() . The emergency controller sits close to the plant and operates only in case of emergency, for example, an attack on the communication line between the plant and controller. The emergency controller could either be a PID controller or optimal controller with the goal to stabilize the system to a particular reference trajectory rE.
. The emergency controller sits close to the plant and operates only in case of emergency, for example, an attack on the communication line between the plant and controller. The emergency controller could either be a PID controller or optimal controller with the goal to stabilize the system to a particular reference trajectory rE.
Suppose there is a time delay attack on the system with delay![]() ; the time delay estimator will estimate the delay
; the time delay estimator will estimate the delay![]() . The cyber-attack detector will use the time delay estimate to perform the following function
. The cyber-attack detector will use the time delay estimate to perform the following function
![]() , (12)
, (12)
where c is a constant between 0 and 1. In case D = 1 an alarm signal is sent to the controller to shut it down and a negative acknowledgement is sent to the emergency controller to stabilize the plant. The control strategy is shown in Figure 1.
We have implemented this method in MATLAB and verified its performance using the load frequency control (LFC) of a two-area distributed power system. In the next section we present and discuss the simulation results.
3. Result
We focus on the LFC system where the controller’s function is to regulate the states of a networked power plant. The multi interconnect LFC dynamic system description can be found in [4] . Here we focus on two-area power system with the attack model as
![]() . (13)
. (13)
The optimal feedback controller is given by
![]() (14)
(14)
and the new state after the attack can be modeled by
![]() (15)
(15)
where ![]() are different/random time-delays and are positive values. When
are different/random time-delays and are positive values. When ![]() are
are
all zero, the system is in its normal operation. An adversary can get access to the communication link and inject a delay attack on the line to direct the system to abnormal operations.
In (13), ![]() denotes the states in the first and second power areas. Then the state vector in the
denotes the states in the first and second power areas. Then the state vector in the ![]() power area is defined as
power area is defined as
![]() (16)
(16)
where![]() ,
, ![]() ,
, ![]() ,
, ![]() and
and ![]() are frequency deviation, power deviation of the ge-
are frequency deviation, power deviation of the ge-
nerator, position value of the turbine, tie-line power flow, and control error on the ![]() power area, respectively [19] . The control error of the
power area, respectively [19] . The control error of the ![]() power area is expressed as
power area is expressed as
![]() (17)
(17)
where ![]() denotes the frequency bias factor.
denotes the frequency bias factor.
In the dynamic model of the two-area LFC (13):
![]() (18)
(18)
![]() (19)
(19)
![]() (20)
(20)
and![]() ,
, ![]() ,
, ![]() and
and ![]() are represented by
are represented by
![]() (21)
(21)
![]() (22)
(22)
![]() (23)
(23)
and
![]() (24)
(24)
where i and j can only be values one and two, ![]() ,
, ![]() ,
, ![]() ,
, ![]() and
and ![]() are the generator moment of inertia, the speed-droop coefficient, generator damping coefficient, the governor time constant, the turbine time constant in the
are the generator moment of inertia, the speed-droop coefficient, generator damping coefficient, the governor time constant, the turbine time constant in the ![]() power area and
power area and ![]() is the stiffness constant between the
is the stiffness constant between the ![]() and the
and the ![]() power areas, respectively.
power areas, respectively.
The analysis starts with the design of an optimal controller for the LFC in the normal operation (i.e., with no attack). Consider the system model described by (13) with the performance index described by
![]() (25)
(25)
where matrix ![]() is positive semi-definite and
is positive semi-definite and ![]() is positive definite. Then, the optimal control problem is to obtain optimal control
is positive definite. Then, the optimal control problem is to obtain optimal control ![]() that minimizes the performance index (25), subject to the dynamic of the system with no time-delay in its states.
that minimizes the performance index (25), subject to the dynamic of the system with no time-delay in its states.
Simulation studies have been conducted to evaluate the effects of TDS attacks on the dynamics of the system and detect TDS attacks to direct the controller to emergency state. By solving the Riccati matrix equation we obtain the close loop control law in the form of state feedback. For the simulations we have used discrete linear-quadratic regulator design from continuous cost function called “lqrd” function in MATLAB 2013a. Table 1 shows parameter values used in this process. We also set both ![]() and
and ![]() to zero.
to zero.
In our simulation, the total simulation time is 50 second and the sampling time is 0.01 s as its common in industrial applications. To show accuracy of our proposed TDS attack detector/tracker, we didn’t send negative acknowledgment to the local controller for the first simulation to only track the injected time delay to the system. The simulation has been done for three different scenarios: 1) single TDS attack on one power area, 2) Simultaneous TDS attack on both power areas, 3) Complex varied TDS attack on both power areas.
1) Single TDS attack to one power area: Here, we considered that adversary attacks the third state of the first power area at time of 2 second for a delay value of 3 seconds and the time delay is increased to 4.5 seconds at time of 7 seconds. Figure 2 shows that the detector accurately tracked and monitored the TDS attack or any
![]()
Table 1. Parameter values for a two-area power system controller design.
natural delay on the system.
2) Simultaneous TDS attack to both power areas: In this scenario, we attack the third state of both power areas. TDS attacks 1 and 2 have been injected to the first and the second power areas respectfully. TDS attack 1 is started at time 2 seconds for value 3 seconds and increased at time 8 seconds to the value of 4.5 seconds. Also TDS attack 2 is started simultaneously with TDS attack 1 for the value of 1.5 seconds and increased to the value of 6 seconds. Figure 3 shows the result.
3) Complex varied TDS attack to both power areas: In the last scenario we injected the TDS attack at different time with different time-delay values. We assume that an adversary injects TDS attack to feedback lines of both power areas. In our simulation, an attacker starts TDS attack to the second power area (third state) at time 1 second for ![]() and then increases it to
and then increases it to ![]() at 20 second. Furthermore, adversary starts to attack the first power area (third state), at 1 second with
at 20 second. Furthermore, adversary starts to attack the first power area (third state), at 1 second with ![]() and increased it to
and increased it to ![]() at 30 second. Figure 4 and Figure 5 show TDS attack tracking real time. Figure 4 shows TDS attack on the third state of the first power area and Figure 5 shows the attack on the same state of the second power area.
at 30 second. Figure 4 and Figure 5 show TDS attack tracking real time. Figure 4 shows TDS attack on the third state of the first power area and Figure 5 shows the attack on the same state of the second power area.
For the second part of our simulation we enabled the emergency controller to show the effect of our proposed technique for overcoming the TDS attack. We assume that an adversary injects TDS attack to the feedback lines of both power areas. In the simulation, a TDS attack was applied to the second power area (the third state) at time of 1 second for ![]() and then increases it to
and then increases it to ![]() at 20 second. Furthermore, adversary starts to attack the first power area (the third state), at 1 second with
at 20 second. Furthermore, adversary starts to attack the first power area (the third state), at 1 second with ![]() and increased it to
and increased it to ![]() at 30 second. We also set the
at 30 second. We also set the ![]() based on stability analysis of LFC system in [4] . We send the negative acknowledgment to emergency controller in the case that detected value of time-delay is more than the maximum allowed time-delay. Figure 6 and Figure 7 show the third state of the first and the second power areas
based on stability analysis of LFC system in [4] . We send the negative acknowledgment to emergency controller in the case that detected value of time-delay is more than the maximum allowed time-delay. Figure 6 and Figure 7 show the third state of the first and the second power areas
![]()
Figure 2. TDS attack detection and tracking for third state of first power area.
![]()
Figure 3. TDS attack detection and tracking for simultaneous TDS attack on both power areas.
![]()
Figure 4. TDS attack detection and tracking for third state of first power area.
![]()
Figure 5. TDS attack detection and tracking for third state of second power area.
![]()
Figure 6. Value position of the turbine system under TDS attack for the first power-area control system.
![]()
Figure 7. Value position of the turbine system under TDS attack for the second power-area control system.
under attack with traditional optimal controller (TOC) and the proposed control technique (PCT) respectively. As it’s clear on the result, the simulated attack makes the system unstable. With the proposed technique, we could overcome TDS attack on the simulated system.
4. Conclusion
In summary, we have demonstrated a simple method for estimating and detecting time delay switch attack on a networked control system. The method relies on a time delay estimator that estimates and tracks time-delays introduced by an adversary. With knowledge of the maximum time delay of the control system, for which the plant remains stable and secure, the time-delay detector compares the estimated time delay to the maximum allowed time delay and issues an alarm signal when the estimated time delay is larger than this value. It also directs the system to an alarm state. In an alarm state, the plant is under the control of the emergency controller, which is local to the plant. The plant remains in this mode until the networked control system state is restored and time-delay switch is eliminated. We think that this method is simple and an inexpensive way to assure that an industrial control system remains stable and secure.
Acknowledgements
The authors would like to thank the Resilient, Autonomous Networked Control Systems (RANCS) group for support during publishing this paper.